Know If Your Data Is Exposed, Before Attackers Use It.
Data leaks don't always start inside your systems — they often begin externally. Compromised credentials, breached databases, exposed tokens, confidential documents and vulnerable infrastructure frequently surface on the dark web long before organizations ever detect them.
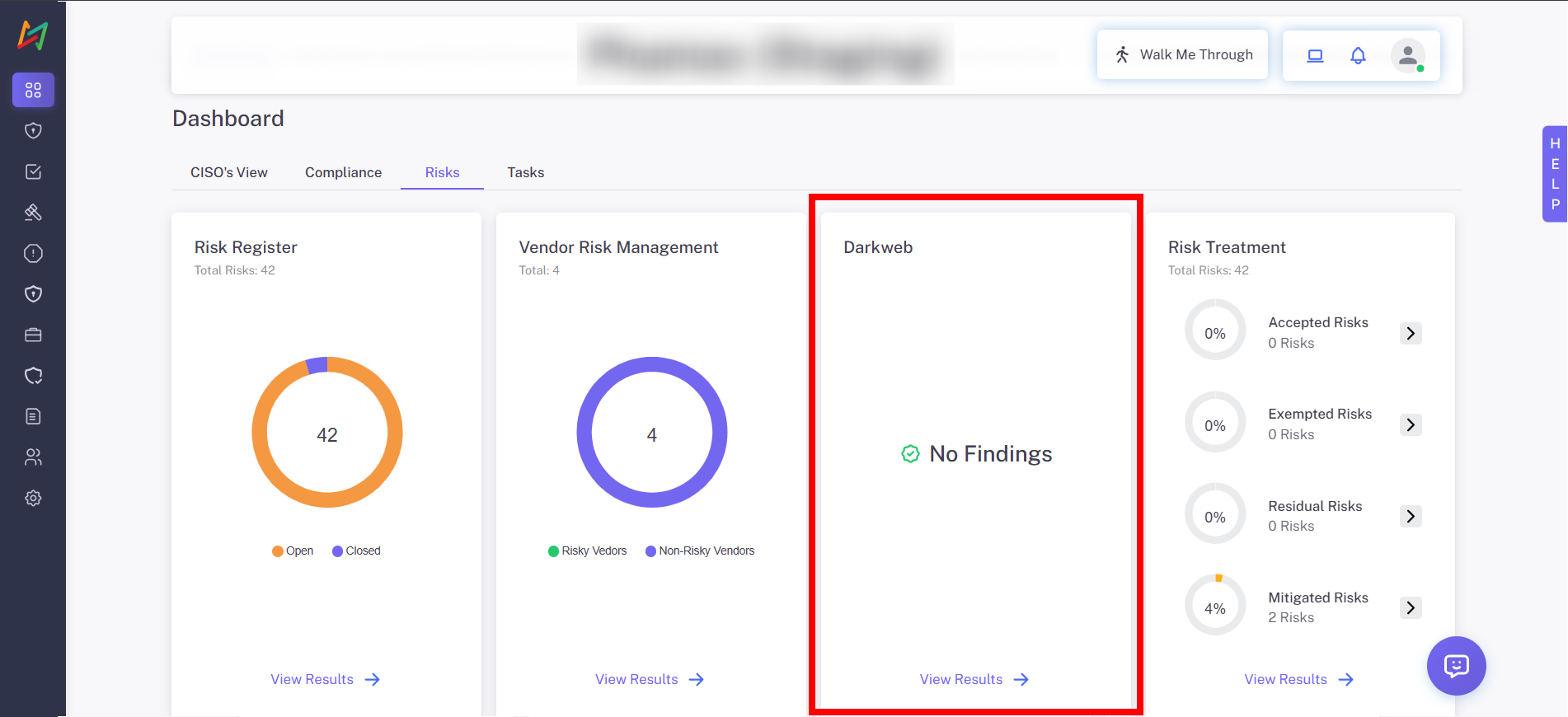
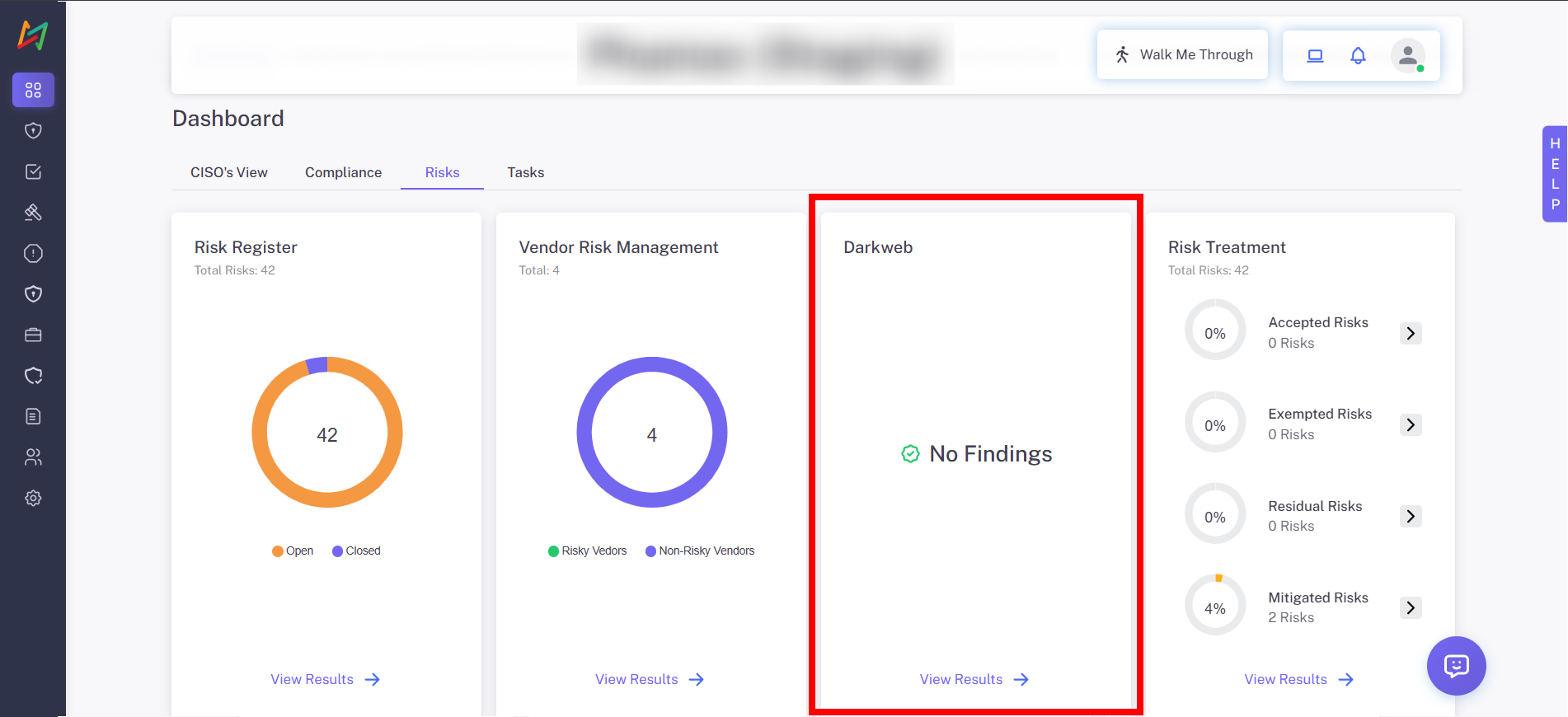
CISOGenie scans breach dumps, black-market forums and threat marketplaces to detect leaked data. Every finding comes with remediation guidance and can be directly converted into a trackable risk within the CISOGenie Risk Register.
Proactive Intelligence
Instant Visibility
No More Silent Exposures
Faster Detection of Breach Indicators
Dark web alerts uncover exposures early, before attackers exploit them.
Reduction in Credential Misuse & Account Takeovers
Leaked passwords and tokens can be rotated immediately with guided actions.
Real-Time Threat Intelligence Feeds
Continuously monitors hidden forums, dumps and marketplaces for your data.
Traceability From Threat to Risk Closure
Every exposure flows into your Risk Register for ownership, mitigation and compliance evidence.
Continuous Monitoring of Corporate & Employee Accounts
Protects both enterprise systems and user identities from unauthorized access.
Key Capabilities
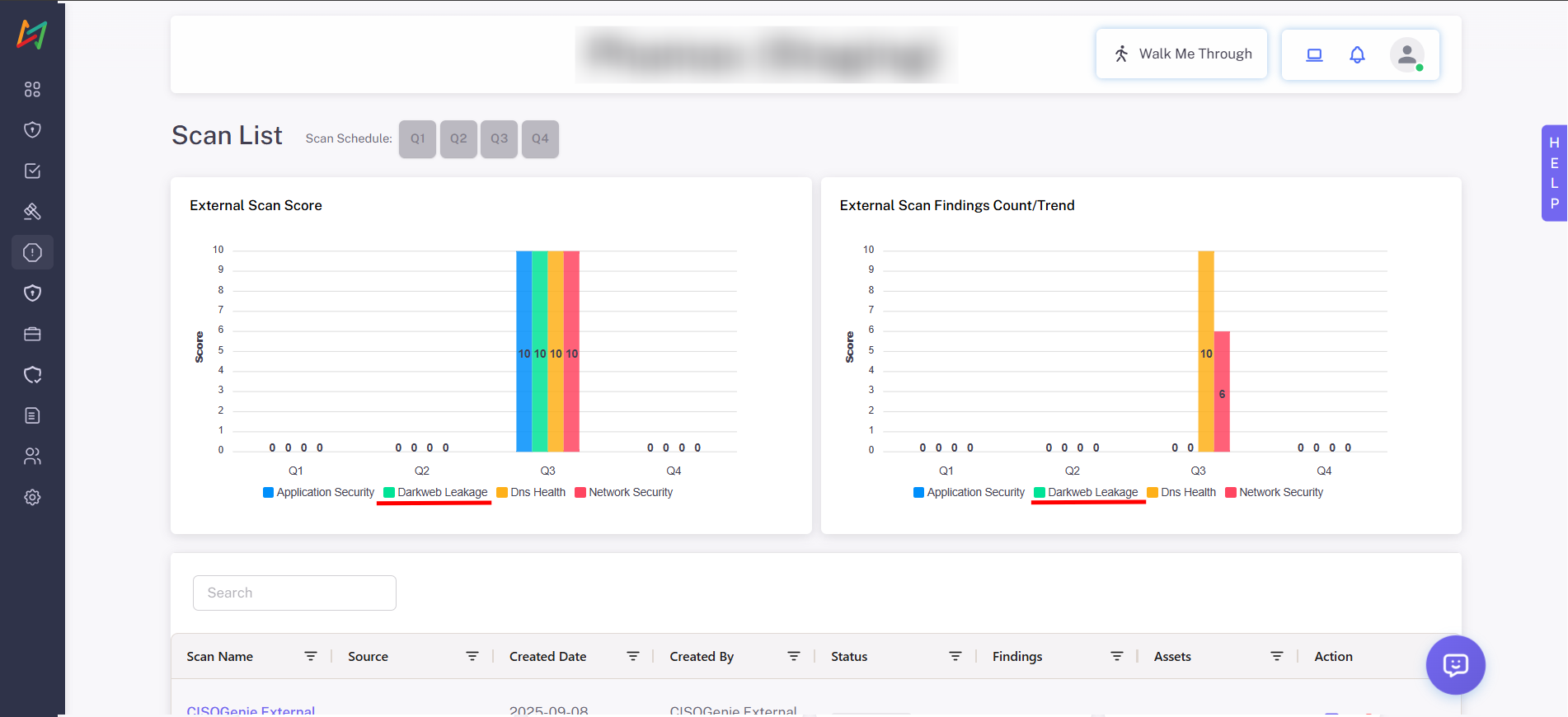
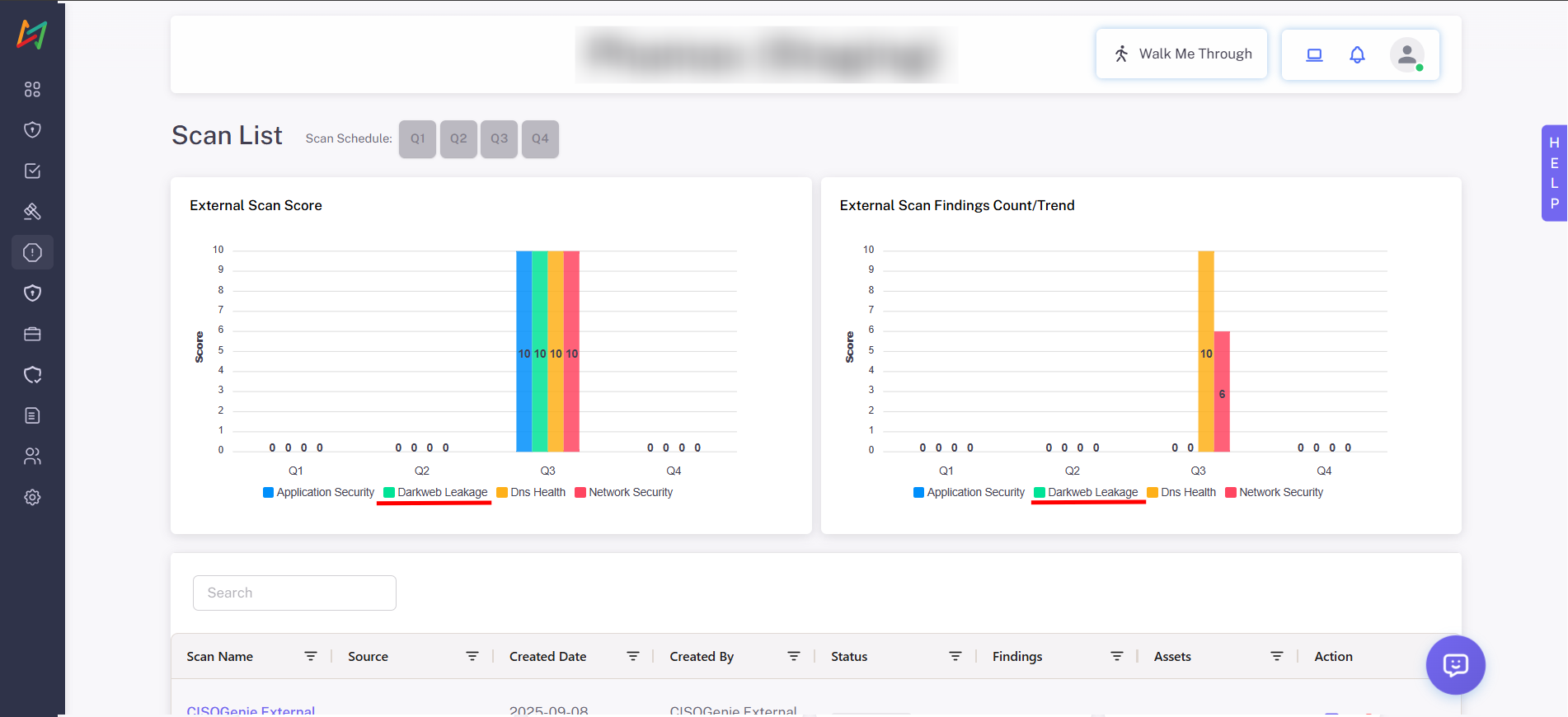
Real-Time External Exposure Score
Access a consolidated risk score based on exposed data, attack surface weaknesses and breach likelihood — updated continuously via external threat feeds.
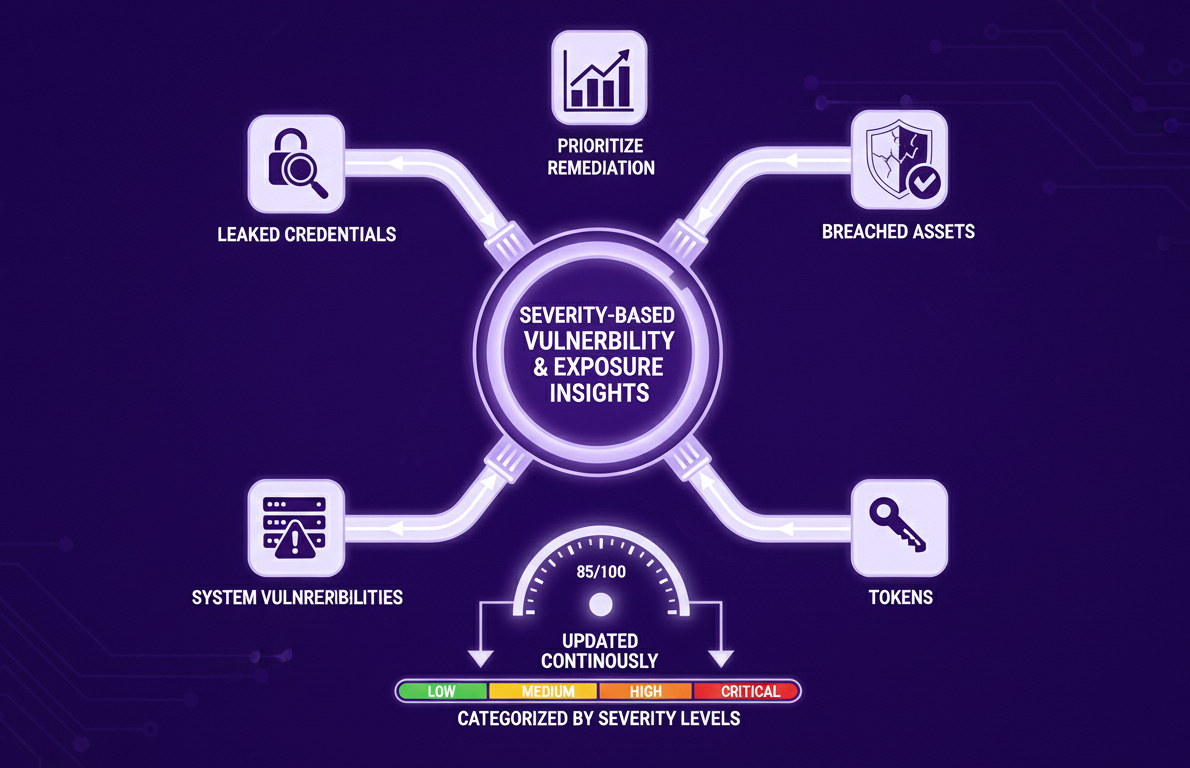
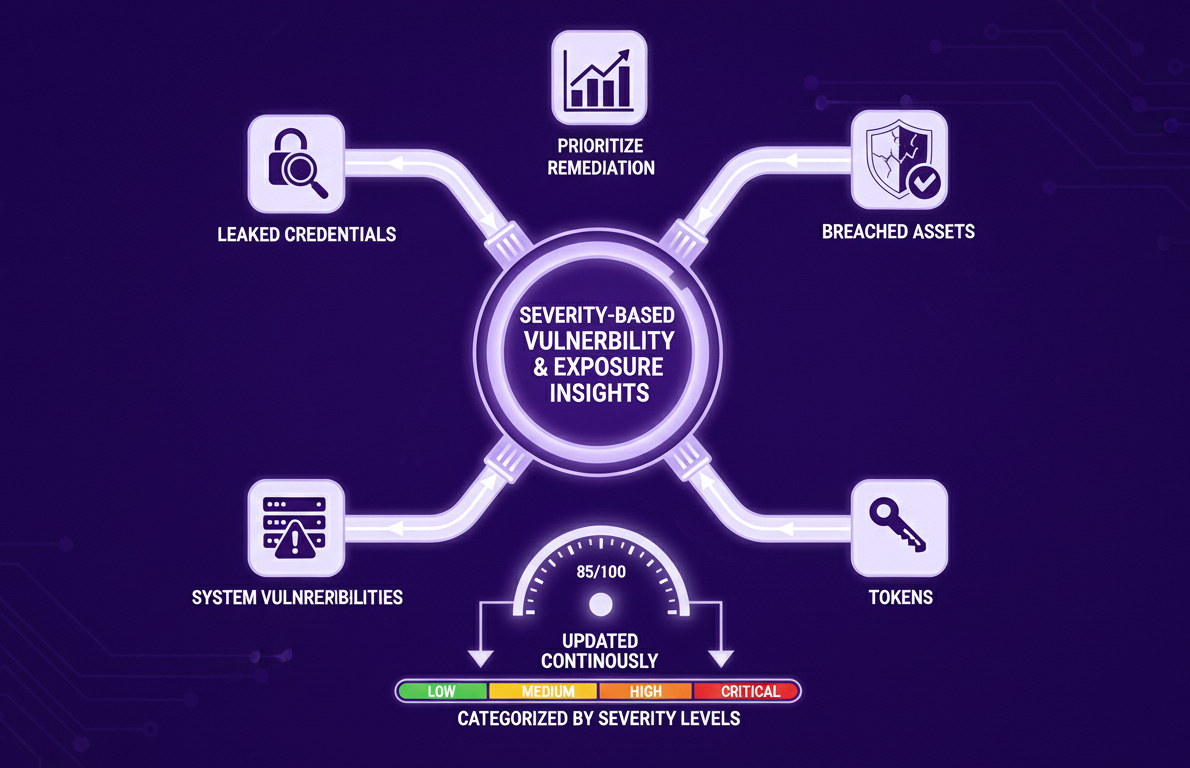
Severity-Based Vulnerability & Exposure Insights
View leaked credentials, breached assets, tokens and system vulnerabilities categorized by severity levels (Low → Critical) to prioritize remediation effectively.
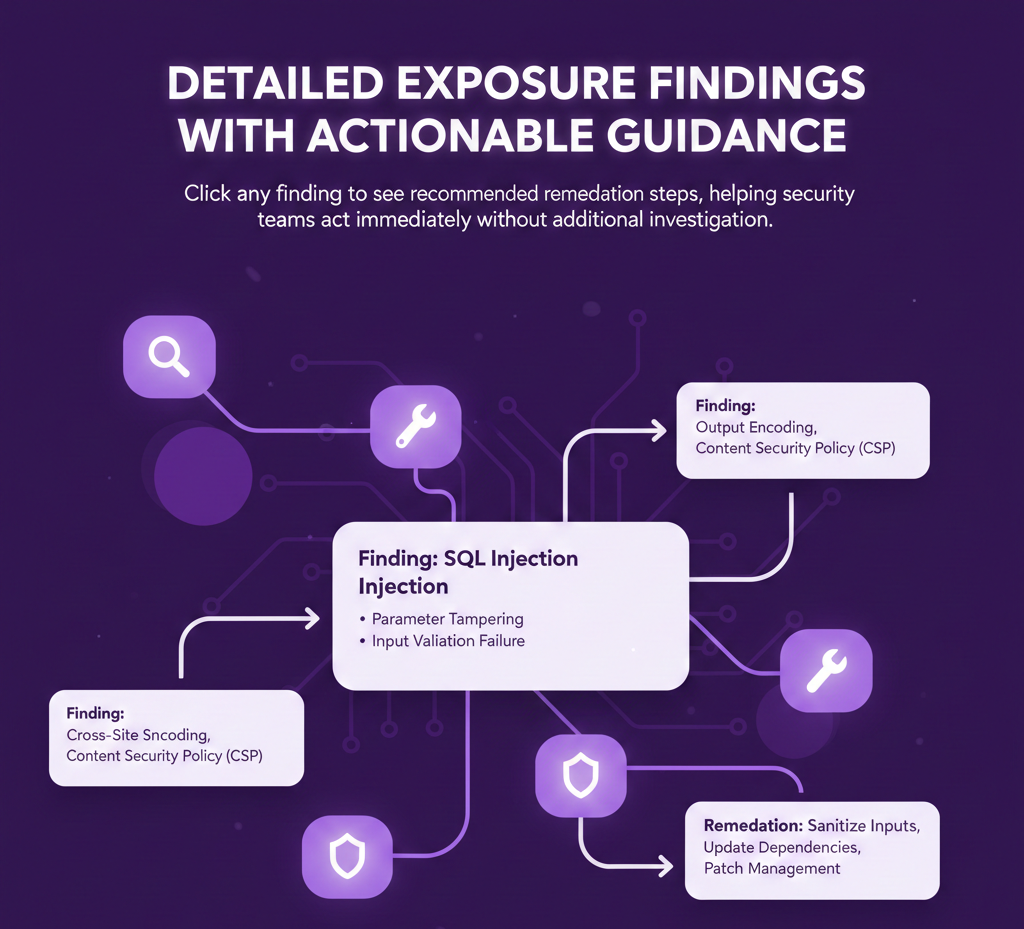
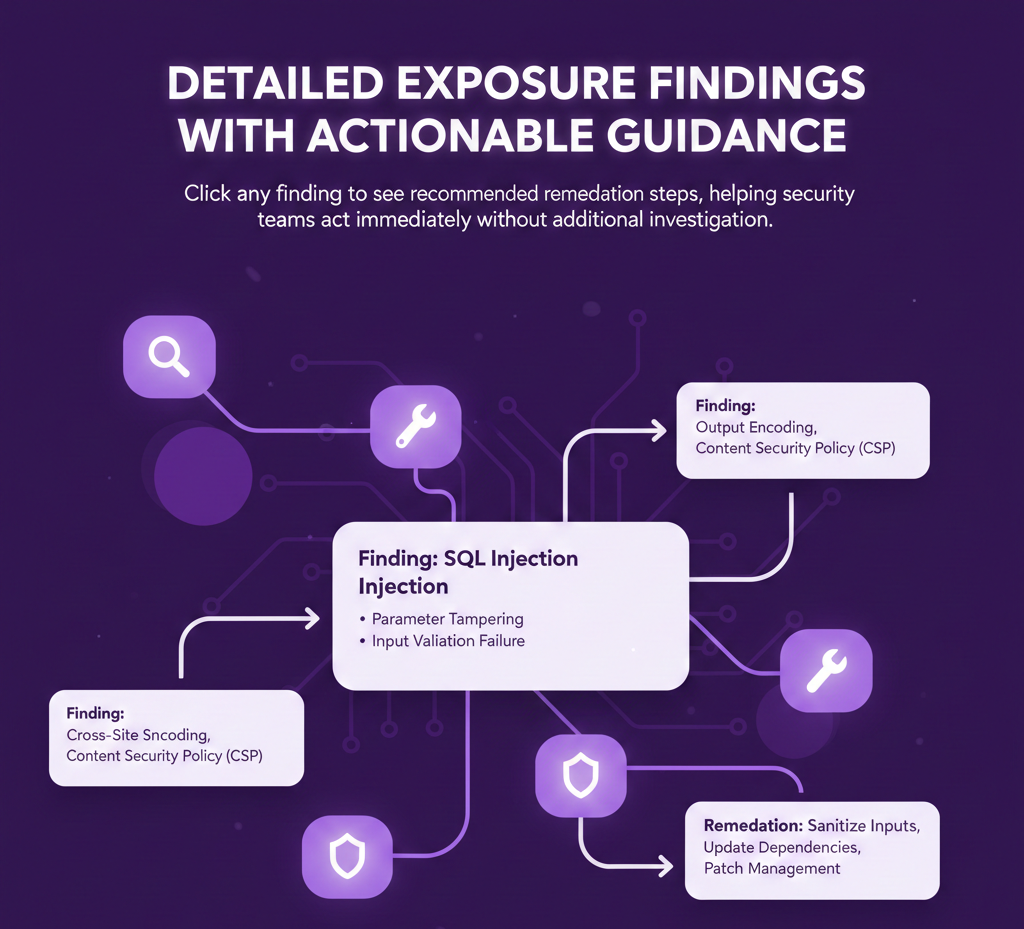
Detailed Exposure Findings with Actionable Guidance
Click any finding to see recommended remediation steps, helping security teams act immediately without additional investigation.


One-Click Risk Conversion
Convert dark web findings into structured risks within the CISOGenie Risk Register — allowing assignment of owners, prioritization and treatment planning.


Full Integration With Risk Lifecycle Management
Every validated exposure gets tracked from Open → Mitigation → Resolved, building evidence trails for audits, compliance and breach prevention reports.
Continuous Scan Intelligence
Monitor corporate and employee accounts, cloud footprints and exposed enterprise data — including email credentials, API keys & tokens, logs, configuration leaks, confidential documents & customer data.


External Attack Surface Analytics
Gain visibility into weaknesses outside your internal environment, reducing blind spots caused by SaaS misconfigurations, outdated cloud assets or forgotten domains.
Why It Matters
Detects Threats Before Breaches Happen
Most breaches are exploited only after stolen data circulates online — early alerts stop attackers at the earliest stage.
Builds External Visibility That Internal Tools Miss
Traditional security tools focus inside your network. CISOGenie adds visibility into what attackers can already see or access.
Strengthens Regulatory Compliance
Key regulations (DPDPA, GDPR, PCI DSS, HIPAA, SOC 2) require proof of controls for breach prevention and timely risk mitigation.
Reduces Identity & Access Fraud
By catching exposures early — organizations prevent impersonation attacks, credential stuffing and unauthorized access.
Enables Proof-Based Risk Governance
Every detected exposure is mapped, owned, resolved and documented with full audit history.
Detect. Alert. Remediate.
Before Attackers Strike.
CISOGenie Dark Web Monitoring continuously scans breach dumps, black-market forums and threat marketplaces to detect leaked data. Every finding comes with remediation guidance and converts directly into a trackable risk within your Risk Register.